CH12: Ransomware Playbook
Introduction
Your SOC receives an alert at 2:47 AM on a Tuesday. The SIEM correlation rule "Mass File Rename Activity" has fired on three file servers simultaneously. Within minutes, a help desk ticket arrives from the overnight operations team: a ransom note has appeared on the desktop of the primary domain controller. The note identifies the attacker group, provides a Tor portal for communication, and gives a 72-hour deadline before stolen data is published on their leak site.
This is not a generic incident. This is ransomware, and it changes everything about how the IR lifecycle operates.
Chapters 5 through 11 built the IR lifecycle piece by piece: preparation, detection, analysis, containment, eradication, recovery, and post-incident review. Each chapter treated the lifecycle phases as general-purpose frameworks applicable to any incident type. This chapter applies that entire lifecycle to a single, specific threat class. Ransomware is the defining threat of the current era because it attacks on multiple fronts simultaneously: it encrypts systems (destroying availability), it exfiltrates data (compromising confidentiality), and it creates a business crisis that forces legal, financial, and executive decision-making under extreme time pressure.
The goal of this chapter is not to repeat the IR lifecycle. It is to build a ransomware-specific playbook that maps directly to the phases you have already learned, with the tactical adjustments, decision gates, and unique considerations that ransomware demands.
Learning Objectives
By the end of this chapter, you will be able to:
- Trace the evolution of ransomware from automated "spray and pray" campaigns to human-operated "Big Game Hunting," and explain how each era changed the defender's calculus.
- Map a modern ransomware intrusion to the Cyber Kill Chain and MITRE ATT&CK frameworks, identifying defender opportunities at each phase.
- Execute a structured ransomware response playbook from initial detection through recovery, applying the IR lifecycle phases (Chapters 5-11) with ransomware-specific modifications.
- Evaluate the legal, financial, and ethical dimensions of the ransom payment decision, including OFAC sanctions screening and the role of cyber insurance.
- Design a ransomware countermeasure strategy built on two pillars: encryption at rest (defeating the data leak) and immutable backups (defeating the lockout).
12.1 Ransomware as a Threat Class
At the mechanism level, ransomware weaponizes encryption against the organization that owns the data. The attacker generates a unique encryption key pair, uses it to encrypt files across the victim's environment, and then demands payment in exchange for the decryption key. Without the key, the data is mathematically unrecoverable.
That is the technical foundation, but the modern ransomware threat has evolved far beyond simple file encryption.
The Triple Extortion Model
Early ransomware groups relied on a single lever: encrypt files and demand payment for the key. If the victim had good backups, they could restore and ignore the demand. Attackers adapted by adding a second lever, and then a third.
Extortion Layer 1: Encryption. The attacker locks the victim's files, disrupting operations. This targets availability. The business cannot function until systems are restored.
Extortion Layer 2: Data Leak. Before encrypting, the attacker exfiltrates sensitive data and threatens to publish it on a dark web leak site if the ransom is not paid. This targets confidentiality. Even if the victim restores from backup (solving Layer 1), the data breach and its regulatory consequences remain.
Extortion Layer 3: External Pressure. Some groups escalate further by launching DDoS attacks against the victim's public-facing infrastructure, contacting the victim's customers or partners directly to inform them of the breach, or reporting the victim to regulators. This creates reputational and operational pressure beyond the original encryption and data theft.
The triple extortion model means that good backups alone no longer neutralize ransomware. A complete defense must address all three layers.

Ransomware-as-a-Service (RaaS)
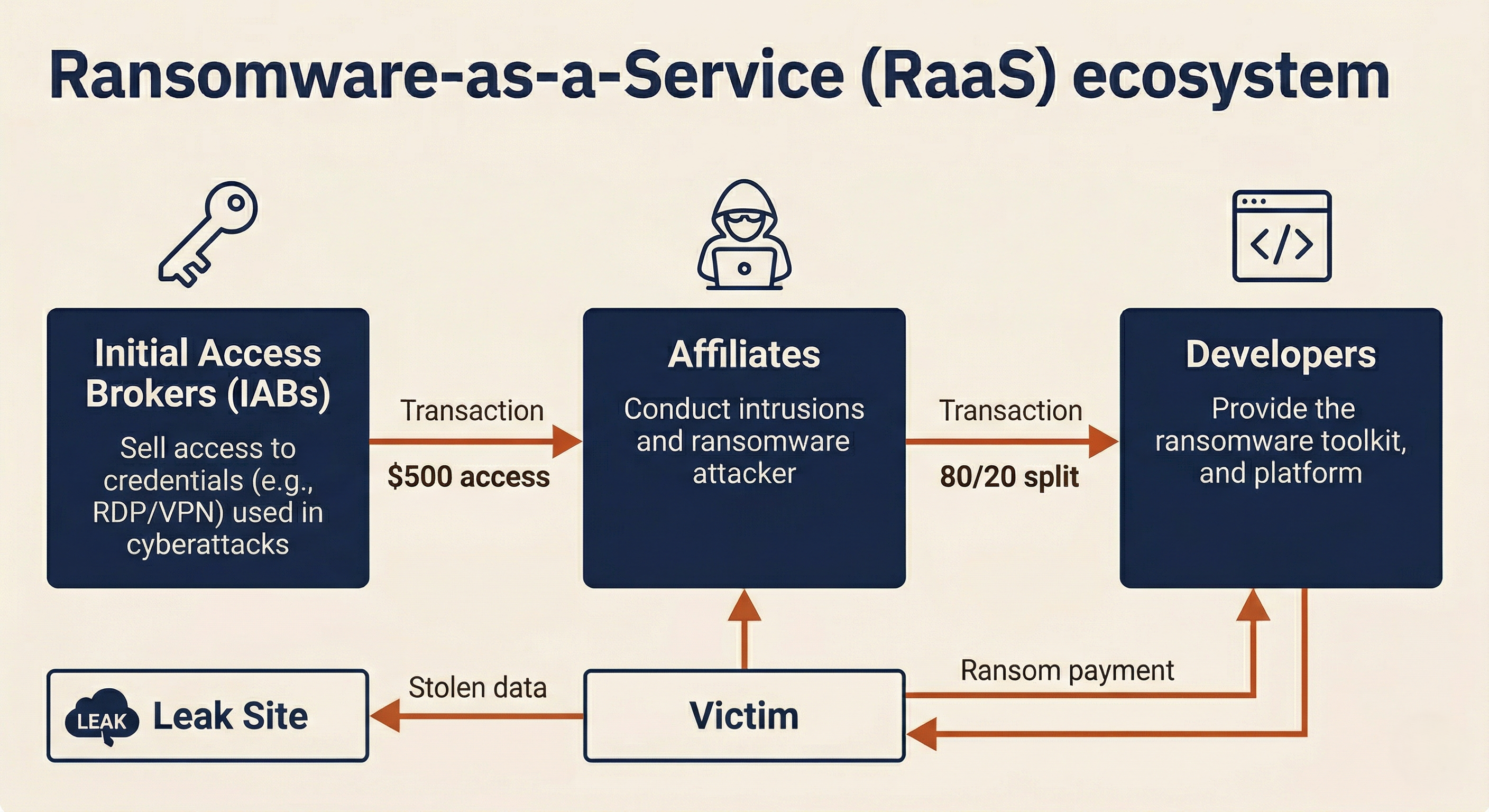
Modern ransomware operates on a franchise model. The organizational structure typically involves three distinct roles:
Developers write and maintain the ransomware code, the encryption engine, the leak site infrastructure, and the victim communication portal. They function as a software company, releasing updates, fixing bugs, and even running "bug bounty" programs where researchers are paid to find flaws in the malware.
Affiliates are the contractors who perform the actual intrusions. They purchase or lease access to the ransomware platform, break into victim networks using their own TTPs, and deploy the ransomware. The affiliate and the developer split the ransom payment, typically 80/20 in the affiliate's favor.
Initial Access Brokers (IABs) specialize in gaining the first foothold. They compromise organizations through phishing, vulnerability exploitation, or credential stuffing, and then sell that access on dark web marketplaces. An affiliate might purchase VPN credentials for $500 and use them to deploy ransomware that generates a $2 million ransom demand.
This division of labor means that the person negotiating with the victim is often not the person who wrote the malware, who in turn is not the person who broke into the network. Each layer operates independently, making disruption difficult and attribution complex.
12.2 Evolution of Ransomware
Understanding how ransomware evolved helps defenders anticipate where it is heading next. The threat has progressed through three distinct eras, each defined by a fundamental shift in attacker tactics.
Era 1: The Automated Age (2013-2017)
The first wave of modern ransomware was exemplified by CryptoLocker (2013). These attacks were automated and indiscriminate. Attackers spammed millions of phishing emails, and whoever clicked was infected. Ransom demands were small, typically $300 to $500 in Bitcoin. The attacker had no knowledge of who the victim was and no interest in maximizing the payment.
The defining characteristic was "spray and pray." If you were infected, it was bad luck, not a targeted operation.
Era 2: The Worm Era (2017)
Two events in 2017 changed the threat permanently.
WannaCry (May 2017) exploited the "EternalBlue" vulnerability in Windows SMB to spread as a self-propagating worm. It infected over 200,000 computers across 150 countries in a matter of hours, crippling the UK's National Health Service and disrupting manufacturing, telecommunications, and logistics worldwide. WannaCry required no human interaction to spread: once it reached a network, it moved at machine speed.
NotPetya (June 2017) appeared to be ransomware but was actually a destructive wiper deployed by Russian military intelligence against Ukraine. It spread globally through a compromised software update for Ukrainian accounting software, causing over $10 billion in total damages. Shipping giant Maersk lost its entire IT infrastructure. NotPetya's ransom payment mechanism was non-functional by design: even victims who paid could not recover their data.
NotPetya demonstrated a critical lesson: not all ransomware is actually ransomware. Some attacks use the appearance of a ransom demand to disguise state-sponsored destruction.
Era 3: Human-Operated "Big Game Hunting" (2019-Present)
The current era is defined by human-operated attacks. Instead of automated spray campaigns, attackers (or their affiliates) manually break into a specific organization, spend days or weeks inside the network (the "dwell time"), identify the most valuable systems and data, destroy or encrypt backups, and then detonate the ransomware for maximum leverage.
Ransom demands in this era routinely reach six to eight figures. The attack is tailored to the victim's ability to pay, often informed by the organization's cyber insurance policy limits, which attackers sometimes discover during their time inside the network.
Ransomware Evolution Reference
| Characteristic | Era 1: Automated (2013-2017) | Era 2: Worm (2017) | Era 3: Human-Operated (2019-Present) |
|---|---|---|---|
| Delivery Method | Mass phishing campaigns | Self-propagating exploit | Targeted intrusion (RDP, VPN, phishing) |
| Target Selection | Random / Indiscriminate | Indiscriminate (worm) | Specific organizations selected for revenue and insurance |
| Attacker Involvement | Fully automated | Automated propagation | Manual (weeks of hands-on-keyboard activity) |
| Ransom Demand | $300 - $500 | $300 (WannaCry) | $100K - $50M+ |
| Extortion Model | Single (encryption only) | Single (encryption only) | Double or Triple (encryption + data leak + pressure) |
| Backup Targeting | No | No | Yes (deliberate backup destruction) |
| Average Dwell Time | Minutes | Minutes | 5-14 days |
Identifying the Strain
Before any discussion of payment or negotiation, the first operational question is: what ransomware strain are you dealing with? The answer determines whether free decryptors exist, what TTPs to expect, and whether the group has a history of honoring (or not honoring) decryption after payment.
Two resources are critical at this stage:
ID Ransomware (id-ransomware.malwarehunterteam.com) allows responders to upload a sample of the ransom note or an encrypted file. The service identifies the ransomware family from its database of over 1,100 strains. It does not decrypt files or perform malware analysis; it identifies the strain so the team knows what they are dealing with.
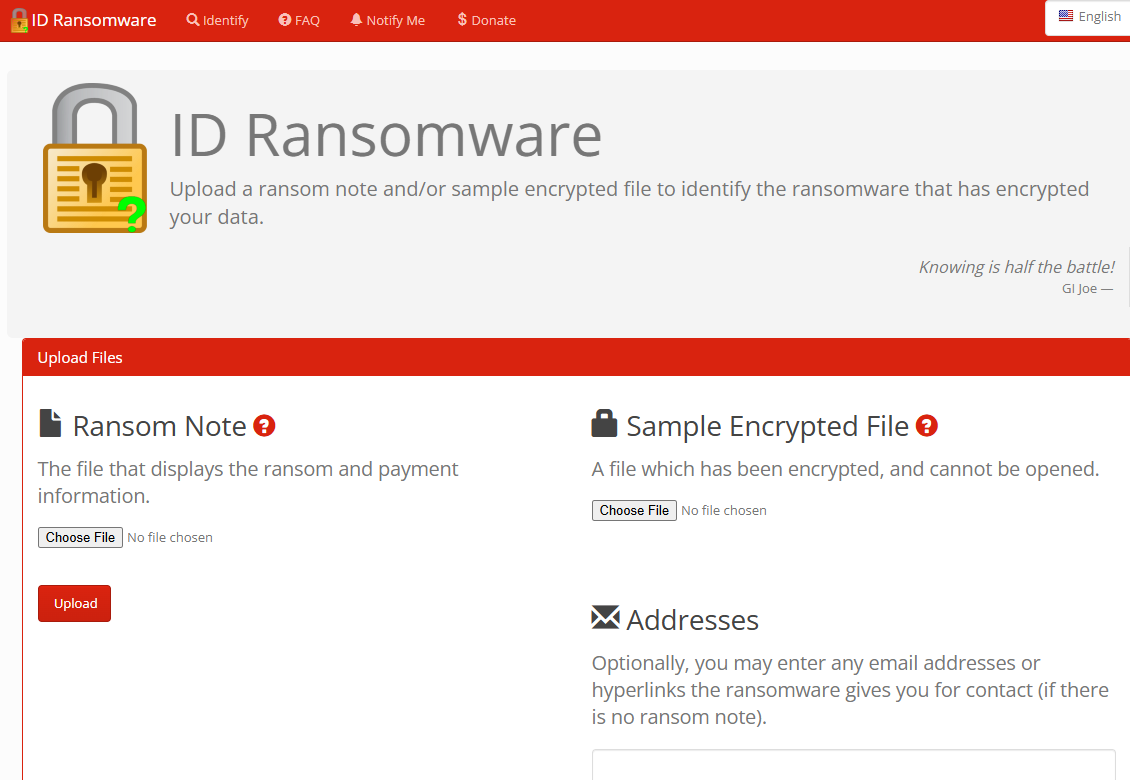
No More Ransom (nomoreransom.org) is a joint initiative between Europol, the Dutch National Police, and cybersecurity vendors. It hosts free decryption tools for ransomware families whose encryption has been broken by researchers or whose keys were seized during law enforcement operations. Checking No More Ransom should be the first step before any payment discussion enters the conversation. If a free decryptor exists, the encryption layer of the extortion is neutralized at zero cost.
Warning
A free decryptor solves the encryption problem (Layer 1) but does not address the data leak threat (Layer 2). If the attacker exfiltrated data before encrypting, the organization still faces the risk of public disclosure regardless of whether the files can be decrypted.
12.3 Anatomy of a Ransomware Attack
Chapters 6 and 7 introduced the Cyber Kill Chain and MITRE ATT&CK as detection and preparation frameworks. This section applies both specifically to ransomware, focusing on what makes a ransomware intrusion distinct from other attack types.
Ransomware Through the Kill Chain
The critical insight for defenders is that encryption, the "boom," happens at the very end of the Kill Chain. The attacker must successfully complete six prior phases before a single file is encrypted. Each of those phases is a detection and disruption opportunity.
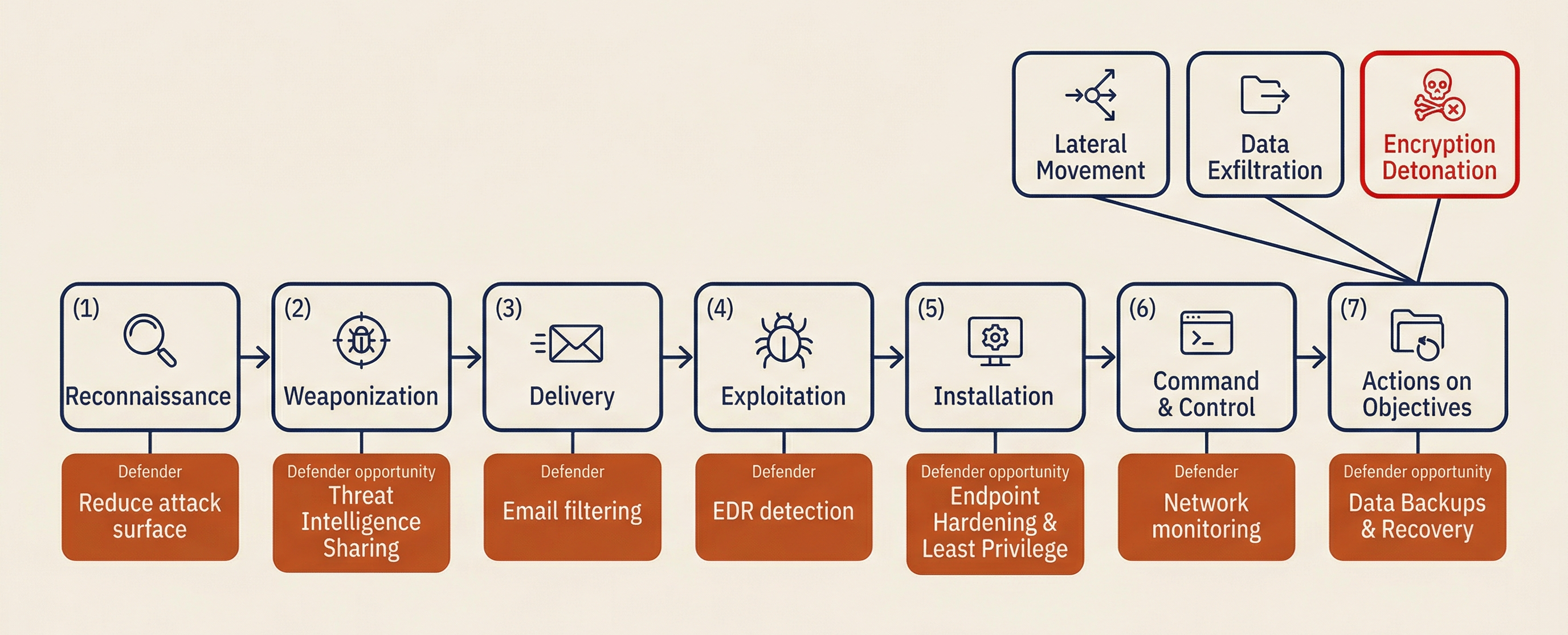
| Kill Chain Phase | Ransomware-Specific Behavior | Defender Opportunity |
|---|---|---|
| 1. Reconnaissance | Attacker (or IAB) scans for exposed RDP, unpatched VPN appliances, or harvests employee emails for phishing | Reduce attack surface: close unnecessary ports, enforce MFA on all external access |
| 2. Weaponization | Affiliate selects a RaaS kit (LockBit, ALPHV/BlackCat, Play) and configures it for the target's OS environment | Threat intelligence: know which RaaS kits are active and what TTPs they use |
| 3. Delivery | Phishing email with malicious macro, exploitation of public-facing application, or use of purchased IAB credentials | Email filtering with sandboxing, patch management, credential monitoring |
| 4. Exploitation | Attacker gains initial foothold on Patient Zero | EDR detection, application allow-listing |
| 5. Installation | Attacker establishes persistence (Cobalt Strike beacon, scheduled task, Registry Run key) and begins lateral movement | EDR behavioral detection, Registry and scheduled task monitoring |
| 6. Command & Control | Compromised host beacons to attacker's C2 infrastructure for instructions and tool downloads | Network monitoring (IDS/IPS), DNS analysis, C2 IP blocklists |
| 7. Actions on Objectives | (a) Lateral movement to high-value targets, (b) Backup destruction, (c) Data exfiltration, (d) Encryption detonation | Network segmentation, backup isolation, DLP, offline/immutable backups |
Case Study: LockBit and MITRE ATT&CK Mapping
To ground these concepts in a real adversary, we examine LockBit, one of the most prolific ransomware operations in history before its partial disruption by law enforcement in February 2024 (Operation Cronos).
LockBit operated as a RaaS platform with a reputation for professionalism that mirrored a legitimate software company. The group maintained a polished victim communication portal, published a public "affiliate code of conduct" (prohibiting attacks on hospitals, for example, though affiliates did not always comply), and ran a bug bounty program offering $1,000 to $1 million for vulnerabilities found in their malware or infrastructure.
The following table maps a typical LockBit affiliate intrusion to the MITRE ATT&CK framework:
| MITRE ATT&CK Tactic | Technique ID | LockBit Affiliate Behavior |
|---|---|---|
| Initial Access | T1190 / T1566 | Exploit public-facing application (unpatched VPN or RDP) or spear-phishing with malicious attachment |
| Execution | T1059.001 | PowerShell scripts to download tools and execute commands |
| Persistence | T1547.001 | Registry Run Keys to ensure malware survives reboot |
| Defense Evasion | T1562.001 | Kill EDR/antivirus processes using tools like GMER, PC Hunter, or custom drivers |
| Credential Access | T1003.001 | Mimikatz or LSASS memory dumping to harvest administrator passwords |
| Lateral Movement | T1021.002 | SMB (Windows Admin Shares) and PsExec to move through the network, blending with normal admin traffic |
| Exfiltration | T1567.002 | StealBit (custom tool) or Rclone to upload data to cloud storage (Mega.nz) before encryption |
| Impact | T1486 | Multi-threaded encryption targeting network shares first, then local drives |
CISA Advisory Reference: For the full technical advisory on LockBit TTPs, see CISA Advisory AA23-165a.
Analyst Perspective
When a SOC analyst receives the first ransomware alert, the ATT&CK mapping for the identified strain becomes the investigation roadmap. If you know the strain is LockBit, you know to hunt for Mimikatz artifacts, PsExec lateral movement, and Rclone exfiltration. You are not searching blindly; you are looking for a known pattern. This is why strain identification (Section 12.2) is one of the first actions in the playbook.
12.4 The Ransomware Response Playbook
This section is the operational core of the chapter. It structures the ransomware response as a decision-gate playbook that maps directly to the IR lifecycle phases from Chapters 5 through 11.
Phase 1: Detection and Initial Triage
Ransomware detection typically comes from one of four sources: an EDR alert on mass file encryption or process termination (the attacker killing security tools), a SIEM correlation rule on abnormal file rename patterns, a user report of a ransom note or inaccessible files, or a help desk spike as multiple users report the same symptoms simultaneously.
The first 15 minutes after detection are critical. The initial triage checklist:
- Scope the impact. How many hosts are affected? Which network segments? Is encryption still active or has it completed?
- Identify the strain. Photograph or copy the ransom note. Upload a sample to ID Ransomware.
- Check No More Ransom. Does a free decryptor exist for this strain?
- Preserve the ransom note. It contains the attacker's communication portal (Tor address), deadline, and sometimes the victim-specific encryption ID needed for decryption.
- Isolate Patient Zero. Apply the containment decision from Chapter 9, Section 9.6: power off, network isolate, or EDR isolate based on whether encryption is still active.
- Activate the CSIRT. Notify the Incident Commander and begin formal incident tracking in the case management system (Chapter 5).
Phase 2: Notification and Mobilization
Ransomware almost always triggers the full organizational response structure from Chapters 4 and 5.
Internal escalation: CSIRT to the Incident Commander, who notifies executive leadership (CISO, CEO, General Counsel). If the scope warrants, activate the Crisis Management Team (Chapter 4).
External notification (within 24 hours of confirmed ransomware):
- Cyber insurance carrier. This is often the single most important early call. The carrier activates pre-approved resources: a professional negotiator (if needed), outside legal counsel experienced in breach response, and forensic investigation support. The "duty to cooperate" clause in most policies requires early notification; late notification can jeopardize coverage.
- Law enforcement. File a report with the FBI's Internet Crime Complaint Center (IC3) at ic3.gov. Contact the local FBI field office if the incident is significant. Report to CISA at cisa.gov/report. Law enforcement may have intelligence on the threat group, access to seized decryption keys, or ongoing operations that the victim can benefit from.
- Outside legal counsel. Breach counsel (often referred to as "breach coach") manages privilege, advises on regulatory obligations, and coordinates the notification process if personal data was compromised.
Regulatory clock awareness: Depending on the jurisdiction and the data involved, mandatory reporting timelines may start from the moment the organization becomes aware of the breach. Key timelines include: SEC registrants face a 4-business-day materiality determination and disclosure requirement, HIPAA-covered entities must notify HHS within 60 days for breaches affecting 500+ individuals, and individual state breach notification laws vary from 30 to 90 days with some requiring notification "without unreasonable delay."
Warning
The regulatory clock starts based on awareness, not on completion of the investigation. Delaying notification because "we are still investigating" is not a valid defense if the organization knew personal data was compromised. Legal counsel should advise on the specific triggers for each applicable regulation.
Phase 3: Containment
Chapter 9 covered containment in depth. For ransomware, the containment priorities shift:
- Stop active encryption. If ransomware is still running, every second costs files. Apply the power-off vs. isolate decision from Chapter 9, Section 9.6.
- Protect unaffected backups. If the attacker has not yet reached the backup infrastructure, isolate it immediately. Disconnect backup servers from the network. Verify that cloud backup credentials have not been compromised.
- Preserve forensic evidence on encrypted hosts. Encrypted hosts contain artifacts needed for the investigation: ransom notes, encryption logs, attacker tools, and potentially the encryption keys in volatile memory (if the host has not been powered off).
- Sever C2 communication. Apply the DNS sinkholing, null-routing, and firewall ACL techniques from Chapter 9, Section 9.3.
Decision gate: Has encryption completed, or is it still active? If encryption is complete, the urgency shifts from "stop the spread" to "preserve evidence and scope the damage." If encryption is still active, speed of isolation takes priority over evidence preservation.
Phase 4: Investigation and Scoping
Chapter 8 covered the general analysis framework. Ransomware investigations add specific questions and artifacts:
Key questions the investigation must answer:
- What was encrypted? (Which hosts, which file shares, which databases?)
- What was exfiltrated? (What data did the attacker steal before encrypting?)
- How did they get in? (The initial access vector must be identified before recovery, or the attacker will return.)
- How long were they in the environment? (Dwell time determines how far back to look for clean backups.)
- Are the backups intact? (Were backup systems targeted or destroyed?)
Ransomware-specific forensic artifacts:
| Artifact | Where to Find It | Why It Matters |
|---|---|---|
| Ransom note | Desktop, root of encrypted drives | Identifies strain, provides attacker contact info, contains victim ID |
| Encrypted file extensions | All affected drives (e.g., .lockbit, .encrypted, .play) | Confirms strain identification |
| Attacker communication portal | Tor address in ransom note | Required for any negotiation; contains leak site countdown |
| Cryptocurrency wallet address | Ransom note or negotiation portal | Used for OFAC screening before any payment discussion |
| Exfiltration tool artifacts | Rclone config files, StealBit logs, Mega.nz upload history | Determines what data was stolen and when |
| Encryption key material | Volatile memory (RAM) on encrypted hosts, if still running | Some strains store the symmetric key in memory during encryption; capturing it may enable free decryption |
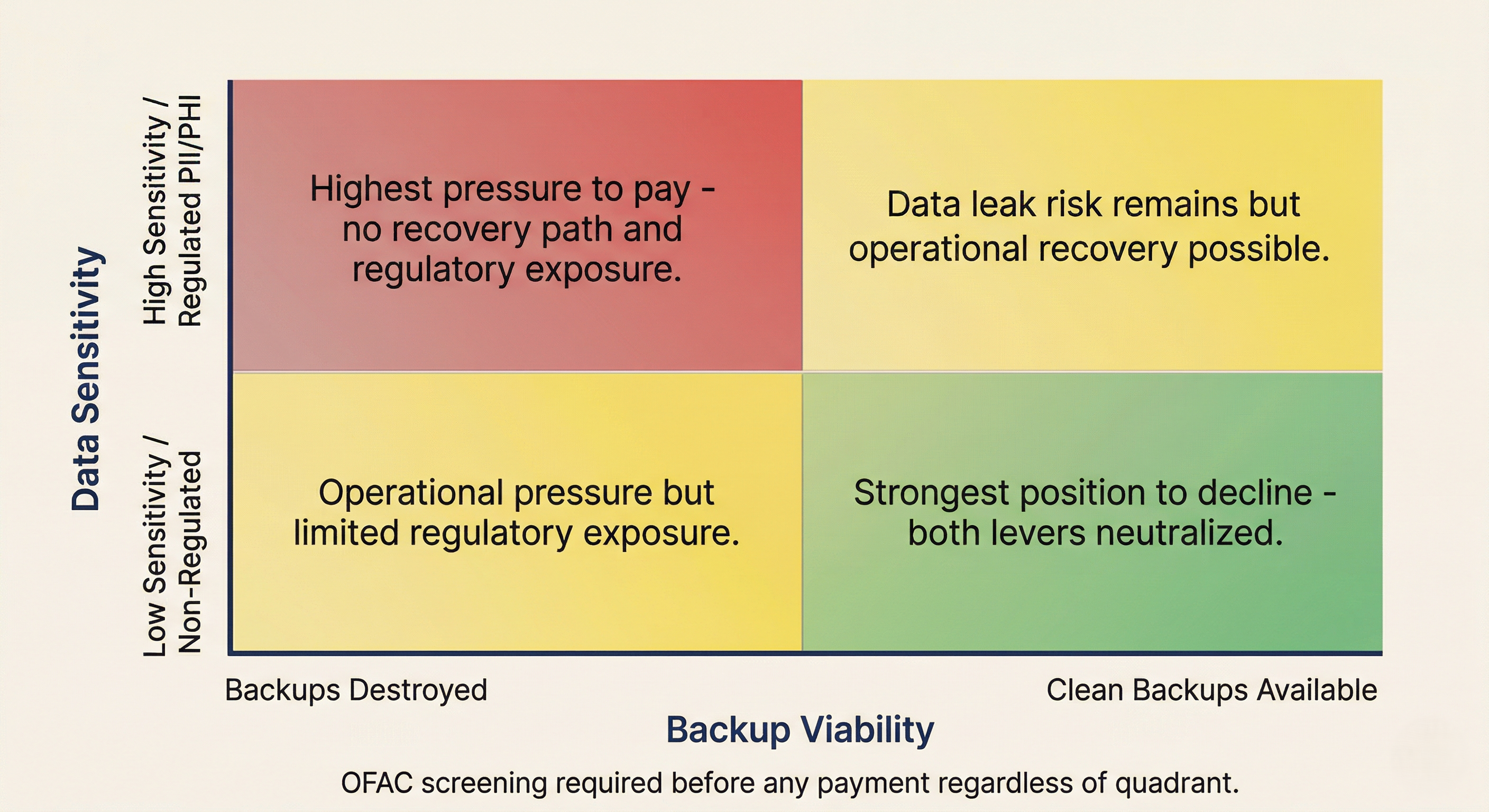
Phase 5: The Payment Decision
The payment decision is a business and legal decision, not a technical one. It should never be made by the IT department alone. The decision authority rests with executive leadership (CEO, Board of Directors, or their designees), informed by Legal Counsel, the CFO, the CISO, and the cyber insurance carrier.
Decision inputs:
| Factor | Pay Consideration | Don't Pay Consideration |
|---|---|---|
| Backup viability | Backups destroyed or encrypted | Clean backups available within acceptable RPO |
| Downtime cost | Cost of extended outage exceeds ransom | Business can sustain the recovery timeline |
| Data sensitivity | Exfiltrated data includes regulated PII, PHI, or trade secrets | Data is non-sensitive or already public |
| Insurance coverage | Policy covers ransom payment | Policy excludes or limits payment |
| Attacker reliability | Group has a track record of providing working decryptors | Group is known to take payment without delivering keys |
| OFAC status | Group is not sanctioned | Group is sanctioned or identity unknown |
OFAC Sanctions: The Legal Red Line
The U.S. Treasury's Office of Foreign Assets Control (OFAC) maintains a list of sanctioned entities, including cybercriminal groups. If the ransomware operator is on the Specially Designated Nationals (SDN) list (examples include Evil Corp and the Lazarus Group), paying the ransom is a federal crime regardless of the circumstances. Ignorance is not a defense.
Before any payment can proceed, the organization must perform a "wallet check": investigating the attacker's cryptocurrency wallet address history against known sanctioned wallets. Professional negotiation firms and breach counsel handle this screening as a standard part of the process.
Cyber Insurance and the Payment Process
In practice, the cyber insurance carrier drives much of the payment logistics if a payment decision is made. The carrier's pre-approved negotiation firm handles communication, the carrier's breach counsel manages legal privilege and regulatory compliance, and the carrier may facilitate the cryptocurrency acquisition and transfer. The victim organization should not attempt to handle payment logistics independently.
Phase 6: Negotiation (If Applicable)
If the organization decides to open a communication channel with the attacker, the process must be handled with discipline and operational security.
Who negotiates: Professional negotiators retained through the cyber insurance carrier or legal counsel. Internal IT staff should never negotiate directly. Negotiation is a specialized skill that requires understanding attacker psychology, stalling tactics, and the economics of the RaaS market.
Communication security: Use a standalone device not connected to the corporate network. Access the attacker's Tor portal from a clean machine. If email is required, use an anonymous provider (ProtonMail). Never communicate from a corporate email address or domain.
Proof of Life: Before any payment discussion, the negotiator must verify that the attacker actually possesses the decryption keys. The standard protocol is to send one or two non-sensitive encrypted files (a generic log file, a stock image) and request that the attacker decrypt and return them. If the attacker cannot produce working decrypted files, they may not actually hold the keys, either because they are scammers impersonating the real group or because their encryption process failed.
Negotiation as a time-buying mechanism: Professional negotiators frequently use the negotiation process to buy time for the investigation and recovery teams. While the negotiator engages the attacker (asking for extensions, requesting more proof, questioning the ransom amount), the technical team is working on backup restoration, evidence collection, and scope assessment. The negotiation channel and the technical response operate in parallel.
Phase 7: Recovery
Chapter 11 covered phased recovery in detail. Ransomware recovery adds specific considerations:
Rebuild, do not restore the OS. Chapter 10 established that reimaging is preferred over cleaning. For ransomware, this is non-negotiable. Restore only the data from backups, onto freshly built systems with hardened baselines.
Scan all backup data before restoration. Attackers with extended dwell times may have planted malware in backup snapshots taken during the days or weeks before detonation. Every restored file should be scanned before being placed on a production system.
Prioritized service bring-up. Follow the BIA tiered recovery from Chapter 11: Active Directory and core identity first, then network security infrastructure, then critical business applications, then general workstations.
Close the initial access vector before reconnecting. If the attacker entered through an unpatched VPN, that VPN must be patched (and its credentials rotated) before any recovered system touches the internet. If the entry was a phishing payload, the email gateway must be hardened. Failing to close the entry point before recovery is an invitation for the attacker to return, often within days.
Data leak response (if the attacker publishes). If the organization declined to pay and the attacker follows through on their threat to publish stolen data, the response shifts to breach notification: regulatory notifications (GDPR, HIPAA, state AGs), individual notification to affected persons, dark web monitoring for the leaked data, and credit monitoring services if PII was exposed. Legal counsel should prepare a public communication strategy in advance so it is ready to deploy immediately if publication occurs.
12.5 Ransomware Countermeasures
The best ransomware playbook is the one you never have to execute. This section addresses the "Left of Boom" controls (borrowing the CFS256 timeline metaphor from Chapter 1) that prevent ransomware from succeeding, or at minimum, limit its impact to a recoverable event.
The modern ransomware business model depends on two conditions: the victim cannot access their data (the encryption lever), and the victim cannot afford to have their data published (the data leak lever). Remove either condition, and the attacker's leverage collapses.
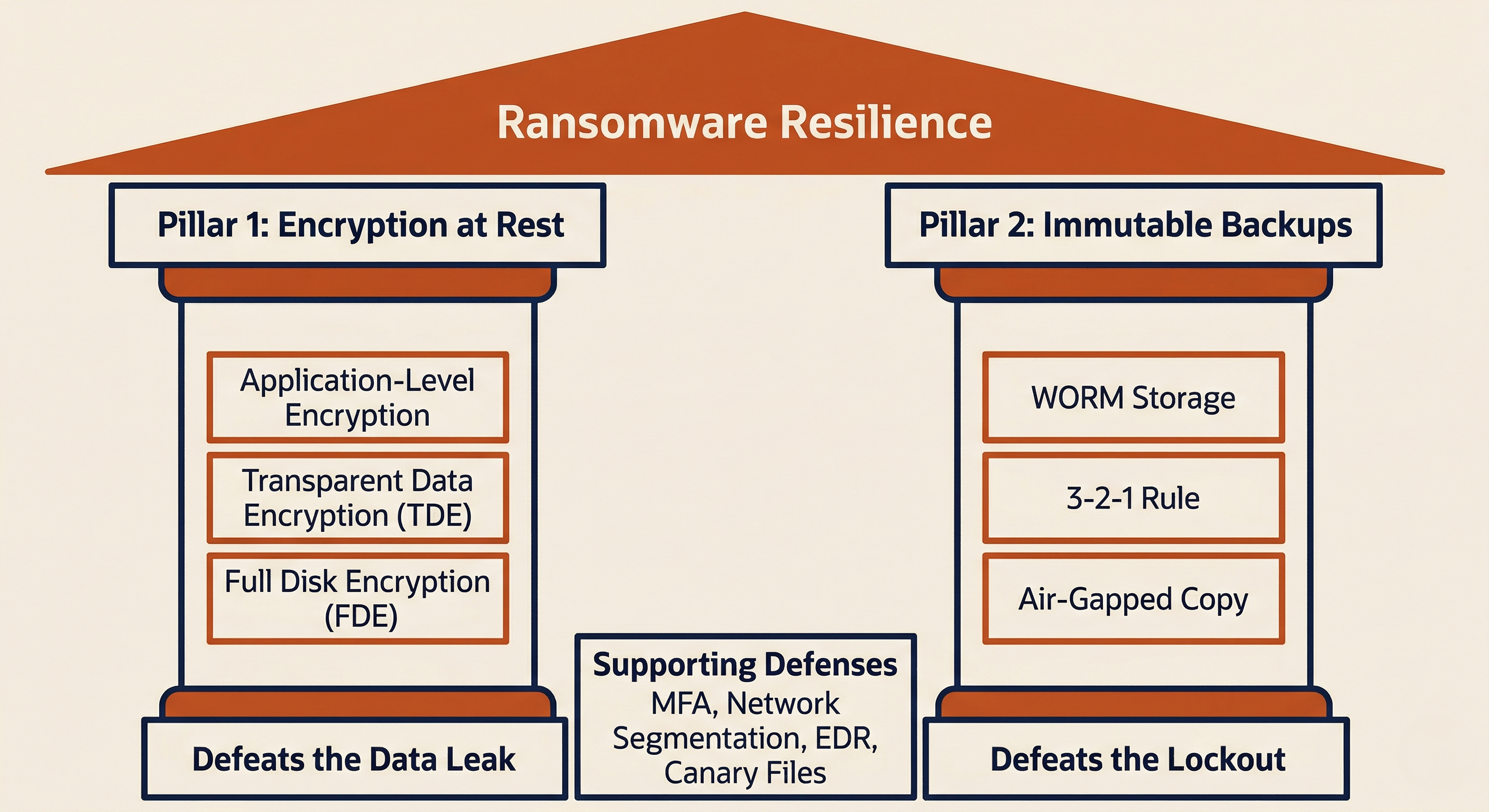
Pillar 1: Encryption at Rest (Defeating the Data Leak)
If the attacker exfiltrates a database that is encrypted at rest with keys they do not possess, the stolen data is unreadable. They cannot credibly threaten to publish it because the leaked files are ciphertext, useless to anyone without the decryption keys.
Application-level encryption encrypts sensitive fields (Social Security numbers, credit card numbers, protected health information) inside the application before they are written to the database. Even if the attacker exports the entire SQL database, the sensitive fields remain encrypted.
Transparent Data Encryption (TDE) encrypts the database files on disk. SQL Server and Oracle both support TDE. This protects against data theft at the file level but does not protect against an attacker who gains authenticated access to the database application itself.
Full Disk Encryption (BitLocker, FileVault, LUKS) protects data on physical drives. This is essential for endpoints (laptops, workstations) where physical theft is a risk, and it provides a defense-in-depth layer for servers.
Pillar 2: Immutable Backups (Defeating the Lockout)
If the organization can restore all encrypted data from clean backups within an acceptable RTO, the encryption lever is neutralized. The attacker cannot pressure the organization to pay for a decryption key it does not need.
The critical word is immutable. Standard backups are insufficient because modern ransomware operators deliberately target backup infrastructure. They search for backup servers, delete shadow copies, and encrypt backup files before detonating the ransomware on production systems.
WORM Storage (Write Once, Read Many) configures backup storage so that once data is written, it cannot be modified or deleted for a defined retention period, even by a root administrator. Cloud implementations include AWS S3 Object Lock and Azure Immutable Blob Storage. On-premises solutions include purpose-built WORM appliances.
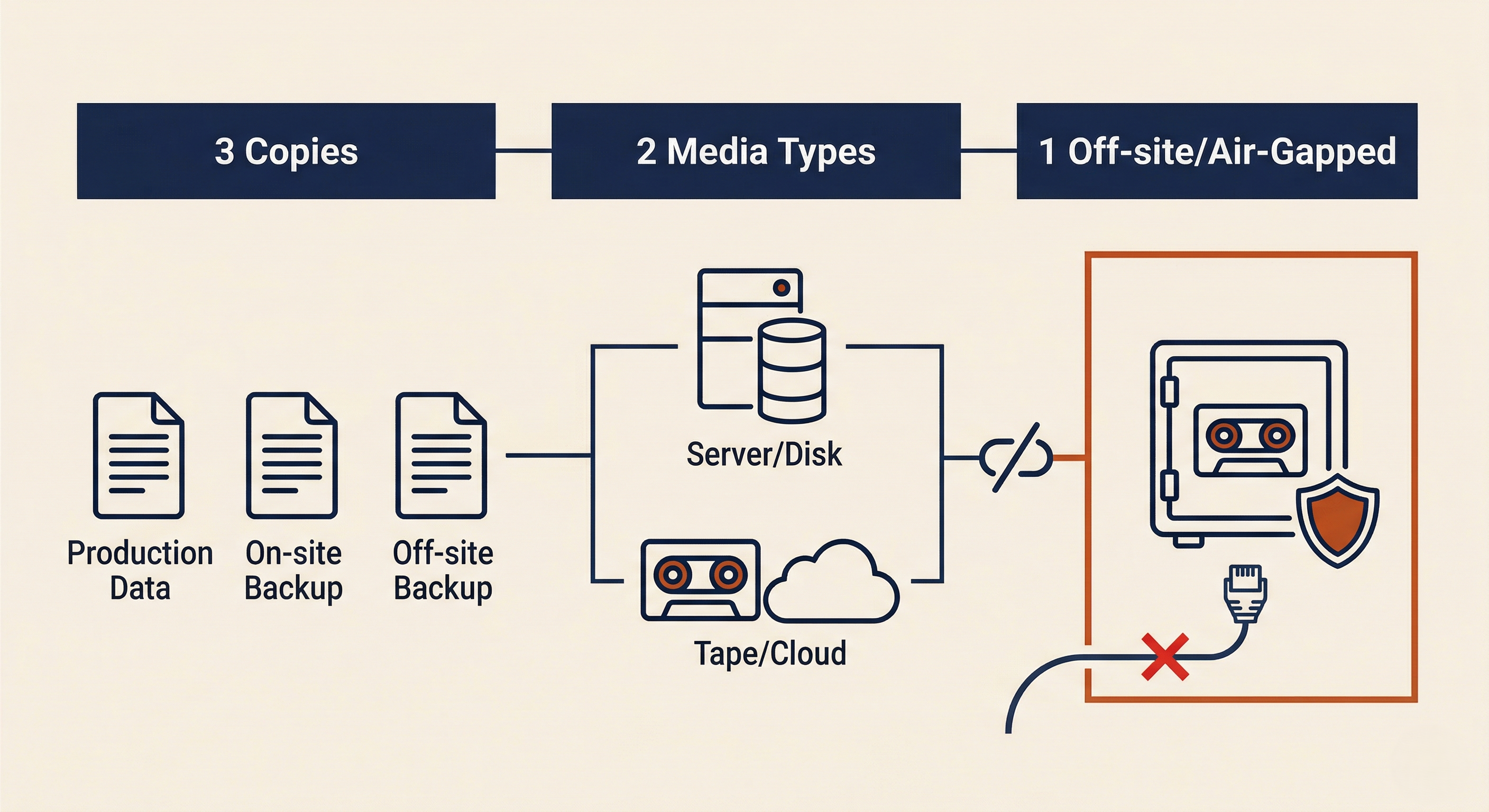
The 3-2-1 Rule remains the gold standard: maintain 3 copies of data, on 2 different media types, with 1 copy offline or air-gapped. An offline tape in a secured vault cannot be reached by any network-based attack. The air-gapped copy is the last line of defense.
Backup testing is not optional. A backup that has never been tested is not a backup; it is an assumption. Regular restore drills (Chapter 3) must verify that backups are complete, uncorrupted, and can be restored within the RTO.
Supporting Defenses
While the two pillars address the attacker's leverage directly, layered defenses reduce the likelihood of a successful intrusion in the first place.
Attack surface reduction: Disable RDP access from the internet (the number one initial access vector for ransomware). Enforce MFA on all external access points: VPNs, email, cloud applications, and remote management tools.
Network segmentation: If a user clicks a phishing link, the infection should be confined to their workstation VLAN. Implement segmentation between workstation, server, and management tiers (Chapter 9 containment matrices). Block workstation-to-workstation SMB traffic to prevent lateral movement.
Endpoint Detection and Response (EDR): Modern EDR platforms detect ransomware behavioral patterns: mass file encryption, process termination of security tools, and known ransomware execution chains. Ransomware canary files (hidden decoy files placed on servers that no legitimate process would access) trigger an automatic isolation response when any process attempts to modify them.
Ransomware Readiness Checklist
| Control | Status | Notes |
|---|---|---|
| Sensitive data encrypted at rest (application, TDE, or FDE) | ☐ | |
| Immutable/WORM backup configured with retention policy | ☐ | |
| Air-gapped or offline backup copy maintained | ☐ | |
| Backup restore tested within last 90 days | ☐ | |
| MFA enforced on all external access (VPN, RDP, email, cloud) | ☐ | |
| RDP not exposed to internet | ☐ | |
| Network segmentation between workstation, server, and management tiers | ☐ | |
| EDR deployed on all endpoints and servers | ☐ | |
| Ransomware canary files deployed on critical file shares | ☐ | |
| Cyber insurance policy current with ransomware coverage confirmed | ☐ | |
| IR playbook for ransomware documented and exercised | ☐ | |
| Breach counsel and negotiation firm pre-identified (via carrier) | ☐ |
Putting It Together: A Ransomware Tabletop
The following tabletop scenario walks through a ransomware incident from detection through recovery. At each decision gate, consider what action you would take and why.
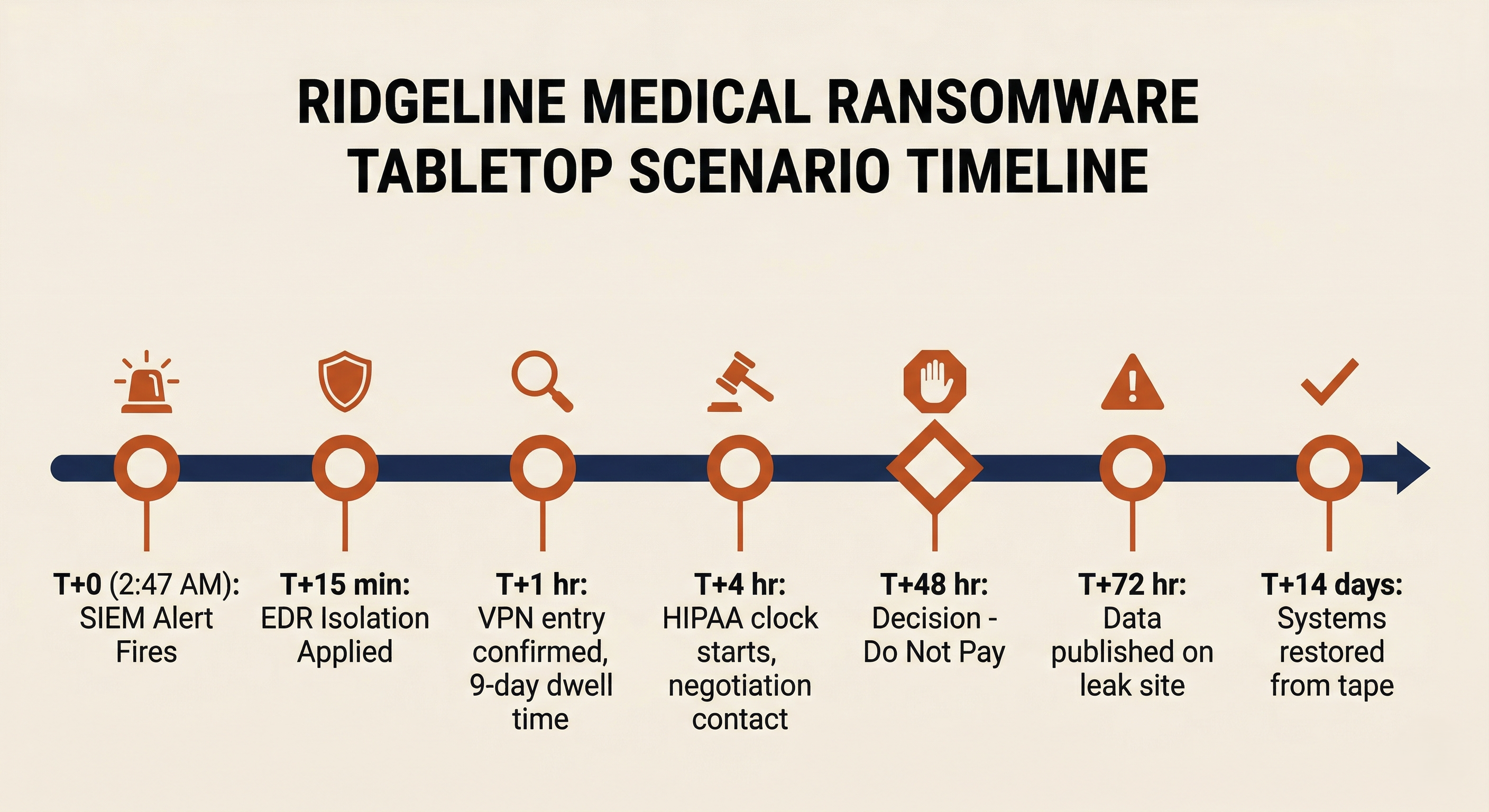
The Organization: Ridgeline Medical Group, a regional healthcare network with 1,200 employees, 15 clinic locations, and a central data center. They are a HIPAA-covered entity. They carry a cyber insurance policy with a $1M ransomware sublimit.
T+0 (Tuesday, 2:47 AM): The overnight SOC analyst receives a SIEM alert: "Mass File Rename Activity" on three file servers hosting patient records (EHR data), billing archives, and medical imaging. EDR fires a secondary alert: "Ransomware Behavior Detected" on one of the file servers.
Decision Gate 1: What is your immediate containment action? Encryption is still active.
T+15 min: The Incident Commander activates the CSIRT. EDR network isolation is applied to all three file servers. Encryption stops. A ransom note on the servers identifies the attacker as Play ransomware group. The note claims 300GB of data was exfiltrated and provides a Tor link and a 72-hour deadline.
Decision Gate 2: Who do you notify in the first hour?
T+1 hour: The CSIRT confirms the following: the attack entered through a compromised VPN credential (no MFA was enforced on the VPN). The attacker had been inside the network for 9 days. Backup servers are intact but the NAS device hosting nightly snapshots has been encrypted. The offsite tape backup (air-gapped, updated weekly) is 6 days old.
Decision Gate 3: Can you recover without paying? What is your RPO gap?
T+4 hours: Legal counsel advises that the exfiltrated data likely includes Protected Health Information (PHI). The HIPAA 60-day notification clock has started. The insurance carrier's negotiation firm has made initial contact with the attacker through the Tor portal and requested Proof of Life. The insurer's forensic team is reviewing the exfiltration artifacts.
Decision Gate 4: The Play group is not an OFAC-sanctioned entity. The ransom demand is $800,000 in Bitcoin. The cost of being offline for the estimated 2-week recovery (using 6-day-old tape backups) is projected at $2.1M in lost revenue plus the cost of manually re-entering 6 days of patient records. What factors does the executive team weigh?
T+48 hours: The executive team, advised by Legal, the CISO, and the insurance carrier, decides not to pay. The rationale: the air-gapped tape backup is viable (6-day RPO is painful but not catastrophic), the organization cannot guarantee the attacker will honor the decryption, and paying does not prevent the data leak. Recovery begins using the phased approach from Chapter 11. The VPN vulnerability is patched and MFA is enforced before any system is reconnected.
T+72 hours: The attacker's deadline passes. Over the following week, the Play group publishes a portion of the stolen data on their leak site. Ridgeline Medical activates its breach notification plan: HHS is notified, individual patient notifications are prepared, and credit monitoring is offered to affected individuals.
T+14 days: All critical systems are restored from tape backup. The 6-day data gap is being reconstructed from paper records and alternate systems. The Post-Incident Review is scheduled for T+21 days.
Analyst Perspective
Notice how the decisions in this scenario connect back to every prior chapter. The containment action (Chapter 9), the investigation scope (Chapter 8), the notification sequence (Chapter 4), the recovery prioritization (Chapter 11), the backup viability (Chapter 3), and the payment decision all operate in parallel, not in sequence. A ransomware incident is the final exam for the entire IR program.
Chapter Summary
Ransomware is the single threat that stress-tests every phase of the IR lifecycle simultaneously: preparation, detection, analysis, containment, eradication, recovery, and post-incident review.
-
Ransomware has evolved through three eras. From automated spray-and-pray campaigns (CryptoLocker), through self-propagating worms (WannaCry, NotPetya), to human-operated Big Game Hunting with double and triple extortion. Modern attacks are manual, targeted, and designed to maximize pressure through encryption, data theft, and external harassment.
-
The Ransomware-as-a-Service model separates development, intrusion, and initial access into distinct roles. This specialization makes the threat more scalable, more professional, and harder to disrupt.
-
Strain identification is an early priority. ID Ransomware and the No More Ransom project should be checked immediately. A free decryptor eliminates the encryption lever entirely.
-
The ransomware playbook maps to the full IR lifecycle. Detection and triage (Chapter 7), notification and mobilization (Chapters 4-5), containment (Chapter 9), investigation (Chapter 8), eradication (Chapter 10), and recovery (Chapter 11) all apply, with ransomware-specific adjustments at each phase.
-
The payment decision is a business and legal decision. It involves executive leadership, legal counsel, and the insurance carrier. OFAC sanctions screening is mandatory. Paying a sanctioned entity is a federal crime regardless of the circumstances.
-
Cyber insurance drives much of the operational response. Early notification to the carrier activates negotiation, legal, and forensic resources. Late notification can jeopardize coverage.
-
Two pillars neutralize the ransomware business model. Encryption at rest defeats the data leak threat (the attacker steals ciphertext). Immutable, air-gapped backups defeat the lockout threat (the organization can restore without paying). Together, they remove both levers of extortion.
-
Recovery must close the initial access vector before reconnecting. If the door the attacker walked through is still open, they will return.
This chapter brought the entire IR lifecycle, built piece by piece over Chapters 5 through 11, together against a single adversary. The ransomware playbook is not a separate process; it is the IR lifecycle applied with precision to the most consequential threat in the field today.